License Key Generation Algorithm C
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. The license key template is a string of characters that represent what actions will be taken when the key is created and decoded. Two types of templates are Bytes and Bits. Bytes are used when the key will be a simple key that does not require a lot of fields and data encoding.
-->Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
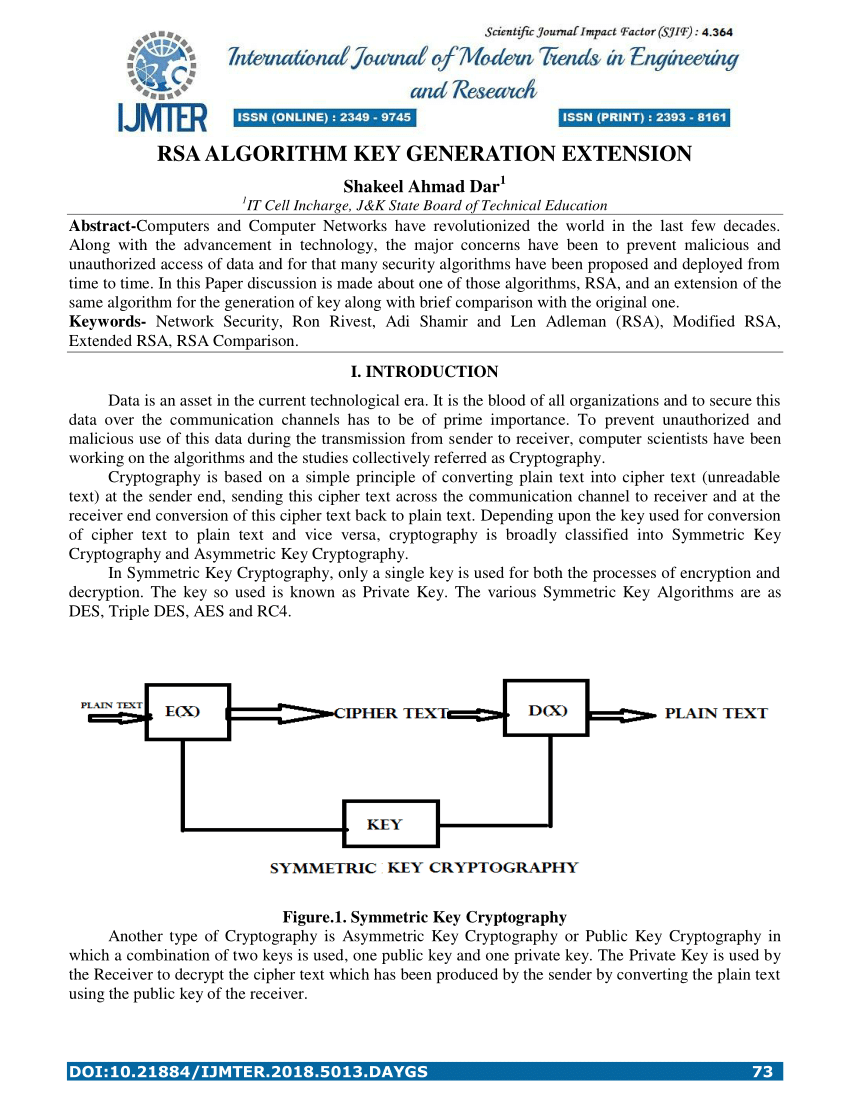
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm. Osx generate new ssh key.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.

Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
Sep 08, 2015 CyberLink PowerDirector 13 Ultimate Keygen full versions is presented in many color schemes and it is latest tool. It also helpful to maintain hardware and software technology and also useful for all type of windows like window 7, 8, 10 etc. CyberLink PowerDirector 13 Full Version is a premium version and available on net free of cost you can. Cyberlink powerdirector 13 product key generator. Jun 24, 2015 Copy & Paste Videos on YouTube and Earn $100 to $300 Per Day - FULL TUTORIAL (Make Money Online) - Duration: 22:51. BIG MARK Recommended for you. Mar 10, 2017 Cyberlink Powerdirector 13 Crack. Cyberlink Powerdirector 13 Crack Full Version useable any window and more you to change design or formats permits downloads. Cyberlink Powerdirector 13 allow to user your work in any way and producing high-quality ultimate work according to your crack designed.Cyberlink Powerdirector 13 very easy to use and friendly interface. Jul 22, 2015 CyberLinkPowerDirector13.rar. Please input captcha to take your serial number. View in text. Similar activation keys. Cyberlink PowerDirector 8.00. CyberLink PowerDirector 8.0. Cyberlink PowerDirector ultra v 7. Cyberlink PowerDirector Ultra64 v10.0Retail.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.
See also
Key management tools for software licensing and activation. C++ and BSD license. Based on crypto++.
Private Key Algorithm
On debian/ubuntu/mint:
Compile using 'make'
License Key Generation Algorithm Chart
genmasterpair - to generate master keys. Keep the private master key in an ultra secure place.
gensecondarypair - to generate a secondary key that is signed by the master key. Keep the secondary master key secure, but if it is compromised, it can be revoked.
genxmllicense and genlicense - generate license files that are signed by the secondary key (which is in turn signed by the master key)
verifyxmllicense and verifylicense - verify signatures in the license file
Adapt the license generation and verification to your own needs.