Dkim Key Generator Dkim For Domain
Create a DKIM TXT record
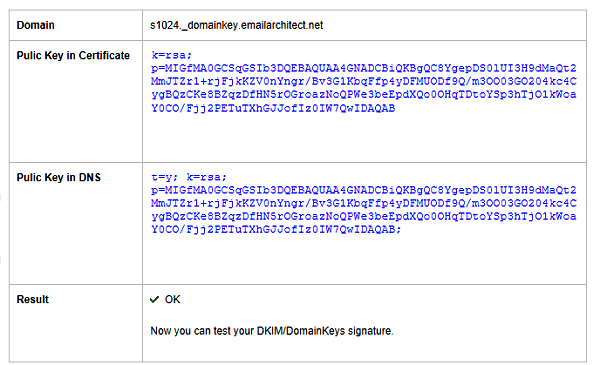
Generate DKIM private and public keys for use with your SocketLabs On-Demand server or plug into any SMTP server that supports DKIM signing. Step 1: Enter in your domain info. Domain Enter the domain that you will send email from. Outbound DKIM uses the private key for your domain to create the signature for each email you send. The signature itself is then placed within the headers of the email. Inbound For inbound email we first verify whether or not the senders domain is setup to use DKIM and if so we then verify the existence and validity of a signature. DKIM record generator is an online tool to create DKIM DNS record to protect your domain from email scam and phishing. Nov 01, 2019 Configure the DNS server with the public key. Create a DKIM TXT record using the domain, selector and the public key. The record will carry the name of the authorized domain attached with the selector prefix, as follows: test-mail.domainkey.example.com. The DKIM entry starts with the k= tag. It stands for ‘Key type’. Enter the selector and domain you have published keys for and press the button. Check a DKIM Core Key Record. Key record: Paste the key record itself. DomainKeys Identified Mail (DKIM) DKIM or DomainKeys Identified Mail (DKIM) is a protocol that uses encryption to verify the sender of an email address. This protocol helps your recipients know that that the email is really coming from your servers, or servers you authorized to send on your behalf, and not from people pretending to be you.
Domain Keys Identified Mail (DKIM) helps you protect your company fromemail spamming and phishing attempts. It provides a method forvalidating a domain name identity that is associated with a messagethrough cryptographic authentication.
For a complete description of DKIM, see the link to recommended DKIM sitesin the “External resources” section at the end of this article.
Note: The method described in this article differs from the way DKIM isset up for Rackspace Hosted Email and Exchange customers. If you are aRackspace Email, Hosted Exchange, or Office 365 customer, contact theRackspace Cloud Office team for help configuring the proper DKIM, DMARC, andSPF records.
The process of setting up DKIM involves the tasks detailedin the following steps:
Choose a DKIM selector.
Generate a public-private key pair.
Publish the selector and public key by creating a DKIM TXT record.
Attach the token to each outgoing email.
What is a DKIM selector?
A selector is specified as an attribute for a DKIM signature and is recorded in the DKIM-Signature header field.
Because DKIM selectors give different DNS query names, the system uses the selector as an additional name component for validation. Under each domain name, there might be one too many unique DKIM DNS records associated with different selectors.
Selectors enable multiple keys under a domain name, which can provide separate signatory controls among departments, date ranges, or third parties acting on behalf of the domain name owner. No two services or products should use the same selector.
A selector can be anything you want, such as a word, number, or a string of letters and numbers.
For example, if you choose oct2019 for your selector, the domain name wouldbecome oct2019._domain.example.com.
Before you begin
Before you log in to the control panel and create a DKIM record, there area couple of things that you need:
Choose a simple, user-defined text string to be your DKIM selector. Theselector is appended to the domain name to help identify the DKIM publickey. See the previous section for more information about choosing aDKIM selector.
Generate a public-private key pair by using a tool such as ssh-keygen onLinux or PuTTYgen on Windows. For help creating key pairs, seeGenerate RSA keys with SSH by using PuTTYgen.
Create a DKIM TXT record
Use the following steps to create a DKIM TXT record in the Cloud ControlPanel:
Log in to the Cloud Control Panel.
In the top navigation bar, click Select a Product > Rackspace Cloud.
Select Networking > Cloud DNS.
Click the gear icon next to the name of an existing domain andselect Add DNS Record.
In the pop-up dialog box, select TXT Record as the record type.
In the Hostname text box, enter the selector text string that you chosein Step 1, followed by the literal string
._domainkey. For example, if youuse the default as the text string, you enterdefault._domainkeyin theHostname text box.Expand the Text box by dragging the corner, and then enter thefollowing information, pasting the public key that you generated in theprevious section after the
p=prompt:When you finish, the TXT record looks similar to the followingexample:
Click Add Record.
The DKIM TXT record is added to your domain.
For instructions about attaching the token to your outgoing email, see theSpecification section at DKIMcore.org.
Related articles
External resources
Experience what Rackspace has to offer.
©2020 Rackspace US, Inc.
Except where otherwise noted, content on this site is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License
-->Summary: This article describes how you use DomainKeys Identified Mail (DKIM) with Office 365 to ensure that destination email systems trust messages sent outbound from your custom domain.
You should use DKIM in addition to SPF and DMARC to help prevent spoofers from sending messages that look like they are coming from your domain. DKIM lets you add a digital signature to outbound email messages in the message header. It may sound complicated, but it's really not. When you configure DKIM, you authorize your domain to associate, or sign, its name to an email message by using cryptographic authentication. Email systems that receive email from your domain can use this digital signature to help determine if incoming email that they receive is legitimate.
Basically, you use a private key to encrypt the header in your domain's outgoing email. You publish a public key to your domain's DNS records that receiving servers can then use to decode the signature. They use the public key to verify that the messages are really coming from you and not coming from someone spoofing your domain.
Dkim Key Generator Dkim For Domain Free
Dkim Key Generator Dkim For Domain Problems
Office 365 automatically sets up DKIM for its initial 'onmicrosoft.com' domains. That means you don't need to do anything to set up DKIM for any initial domain names (for example, litware.onmicrosoft.com). For more information about domains, see Domains FAQ.
You can choose to do nothing about DKIM for your custom domain too. If you don't set up DKIM for your custom domain, Office 365 creates a private and public key pair, enables DKIM signing, and then configures the Office 365 default policy for your custom domain. While this is sufficient coverage for most Office 365 customers, you should manually configure DKIM for your custom domain in the following circumstances:
You have more than one custom domain in Office 365
You're going to set up DMARC too (recommended)
You want control over your private key
You want to customize your CNAME records
You want to set up DKIM keys for email originating out of a third-party domain, for example, if you use a third-party bulk mailer.
In this article:
How DKIM works better than SPF alone to prevent malicious spoofing in Office 365
SPF adds information to a message envelope but DKIM actually encrypts a signature within the message header. When you forward a message, portions of that message's envelope can be stripped away by the forwarding server. Since the digital signature stays with the email message because it's part of the email header, DKIM works even when a message has been forwarded as shown in the following example.
In this example, if you had only published an SPF TXT record for your domain, the recipient's mail server could have marked your email as spam and generated a false positive result. The addition of DKIM in this scenario reduces false positive spam reporting. Because DKIM relies on public key cryptography to authenticate and not just IP addresses, DKIM is considered a much stronger form of authentication than SPF. We recommend using both SPF and DKIM, as well as DMARC in your deployment.
The nitty gritty: DKIM uses a private key to insert an encrypted signature into the message headers. The signing domain, or outbound domain, is inserted as the value of the d= field in the header. The verifying domain, or recipient's domain, then use the d= field to look up the public key from DNS and authenticate the message. If the message is verified, the DKIM check passes.
Manually upgrade your 1024-bit keys to 2048-bit DKIM encryption keys
Since both 1024 and 2048 bitness are supported for DKIM keys, these directions will tell you how to upgrade your 1024-bit key to 2048. The steps below are for two use-cases, please choose the one that best fits your configuration.
- When you already have DKIM configured, you rotate bitness as follows:
- Connect to Office 365 workloads via PowerShell. (The cmdlet comes from Exchange Online.)
- And then execute the following cmdlet:
Rotate-DkimSigningConfig -KeySize 2048 -Identity {Guid of the existing Signing Config}
- Or for a new implementation of DKIM:
- Connect to Office 365 workloads via PowerShell. (This is an Exchange Online cmdlet.)
- Execute the following cmdlet:
New-DkimSigningConfig -DomainName {Domain for which config is to be created} -KeySize 2048 -Enabled $True
Stay connected to Office 365 to verifyEaseus data recovery wizard license key generator reddiu. the configuration.
- Execute the cmdlet:
Get-DkimSigningConfig fl
Tip
This new 2048-bit key takes effect on the RotateOnDate, and will send emails with the 1024-bit key in the interim. After four days, you can test again with the 2048-bit key (that is, once the rotation takes effect to the second selector).
If you want to rotate to the second selector, your options are a) let the Office 365 service rotate the selector and upgrade to 2048-bitness within the next 6 months, or b) after 4 days and confirming that 2048-bitness is in use, manually rotate the second selector key by using the appropriate cmdlet listed above.
Steps you need to do to manually set up DKIM in Office 365
To configure DKIM, you will complete these steps:
Publish two CNAME records for your custom domain in DNS
For each domain for which you want to add a DKIM signature in DNS, you need to publish two CNAME records.
Run the following commands to create the selector records:
Create CNAMEs referenced in Get-DkimSigningConfig output
Office 365 performs automatic key rotation using the two records that you establish. If you have provisioned custom domains in addition to the initial domain in Office 365, you must publish two CNAME records for each additional domain. So, if you have two domains, you must publish two additional CNAME records, and so on.
Use the following format for the CNAME records.
Important
If you are one of our GCC High customers, we calculate domainGuid differently! Instead of looking up the MX record for your initialDomain to calculate domainGuid, instead we calculate it directly from the customized domain. For example, if your customized domain is 'contoso.com' your domainGuid becomes 'contoso-com', any periods are replaced with a dash. So, regardless of what MX record your initialDomain points to, you'll always use the above method to calculate the domainGuid to use in your CNAME records.
Where:
For Office 365, the selectors will always be 'selector1' or 'selector2'.
domainGUID is the same as the domainGUID in the customized MX record for your custom domain that appears before mail.protection.outlook.com. For example, in the following MX record for the domain contoso.com, the domainGUID is contoso-com:
initialDomain is the domain that you used when you signed up for Office 365. Initial domains always end in onmicrosoft.com. For information about determining your initial domain, see Domains FAQ.
For example, if you have an initial domain of cohovineyardandwinery.onmicrosoft.com, and two custom domains cohovineyard.com and cohowinery.com, you would need to set up two CNAME records for each additional domain, for a total of four CNAME records.
Note
It's important to create the second record, but only one of the selectors may be available at the time of creation. In essence, the second selector might point to an address that hasn't been created yet. We still recommended that you create the second CNAME record, because your key rotation will be seamless and you won't need to do any manual steps yourself.
Enable DKIM signing for your custom domain in Office 365
Once you have published the CNAME records in DNS, you are ready to enable DKIM signing through Office 365. You can do this either through the Microsoft 365 admin center or by using PowerShell.
To enable DKIM signing for your custom domain through the admin center
Sign in to Office 365 with your work or school account.
Select the app launcher icon in the upper-left and choose Admin.
In the lower-left navigation, expand Admin and choose Exchange.
Go to Protection > dkim.
Select the domain for which you want to enable DKIM and then, for Sign messages for this domain with DKIM signatures, choose Enable. Repeat this step for each custom domain.
To enable DKIM signing for your custom domain by using PowerShell
Connect to Exchange Online PowerShell.
Run the following command:
Where domain is the name of the custom domain that you want to enable DKIM signing for.
For example, for the domain contoso.com:
To Confirm DKIM signing is configured properly for Office 365
Wait a few minutes before you follow these steps to confirm that you have properly configured DKIM. This allows time for the DKIM information about the domain to be spread throughout the network.
Send a message from an account within your Office 365 DKIM-enabled domain to another email account such as outlook.com or Hotmail.com.
Do not use an aol.com account for testing purposes. AOL may skip the DKIM check if the SPF check passes. This will nullify your test.
Open the message and look at the header. Instructions for viewing the header for the message will vary depending on your messaging client. For instructions on viewing message headers in Outlook, see View e-mail message headers.
The DKIM-signed message will contain the host name and domain you defined when you published the CNAME entries. The message will look something like this example:
Look for the Authentication-Results header. While each receiving service uses a slightly different format to stamp the incoming mail, the result should include something like DKIM=pass or DKIM=OK.
To configure DKIM for more than one custom domain in Office 365
If at some point in the future you decide to add another custom domain and you want to enable DKIM for the new domain, you must complete the steps in this article for each domain. Specifically, complete all steps in What you need to do to manually set up DKIM in Office 365.
Disabling the DKIM signing policy for a custom domain in Office 365
Disabling the signing policy does not completely disable DKIM. After a period of time, Office 365 will automatically apply the default Office 365 policy for your domain. For more information, see Default behavior for DKIM and Office 365.
To disable the DKIM signing policy by using Windows PowerShell
Connect to Exchange Online PowerShell.
Run one of the following commands for each domain for which you want to disable DKIM signing.
For example:
Or
Where number is the index of the policy. For example:
Default behavior for DKIM and Office 365
If you do not enable DKIM, Office 365 automatically creates a 1024-bit DKIM public key for your default domain and the associated private key which we store internally in our datacenter. By default, Office 365 uses a default signing configuration for domains that do not have a policy in place. This means that if you do not set up DKIM yourself, Office 365 will use its default policy and keys it creates in order to enable DKIM for your domain.
Also, if you disable DKIM signing after enabling it, after a period of time, Office 365 will automatically apply the Office 365 default policy for your domain.
In the following example, suppose that DKIM for fabrikam.com was enabled by Office 365, not by the administrator of the domain. This means that the required CNAMEs do not exist in DNS. DKIM signatures for email from this domain will look something like this:
In this example, the host name and domain contain the values to which the CNAME would point if DKIM-signing for fabrikam.com had been enabled by the domain administrator. Eventually, every single message sent from Office 365 will be DKIM-signed. If you enable DKIM yourself, the domain will be the same as the domain in the From: address, in this case fabrikam.com. If you don't, it will not align and instead will use your organization's initial domain. For information about determining your initial domain, see Domains FAQ.
Set up DKIM so that a third-party service can send, or spoof, email on behalf of your custom domain
Some bulk email service providers, or software-as-a-service providers, let you set up DKIM keys for email that originates from their service. This requires coordination between yourself and the third-party in order to set up the necessary DNS records. No two organizations do it exactly the same way. Instead, the process depends entirely on the organization.
An example message showing a properly configured DKIM for contoso.com and bulkemailprovider.com might look like this:
In this example, in order to achieve this result:
Bulk Email Provider gave Contoso a public DKIM key.
Contoso published the DKIM key to its DNS record.
When sending email, Bulk Email Provider signs the key with the corresponding private key. By doing so, Bulk Email Provider attached the DKIM signature to the message header.
Receiving email systems perform a DKIM check by authenticating the DKIM-Signature d=<domain> value against the domain in the From: (5322.From) address of the message. In this example, the values match:
sender@contoso.com
d=contoso.com
Next steps: After you set up DKIM for Office 365
Although DKIM is designed to help prevent spoofing, DKIM works better with SPF and DMARC. Once you have set up DKIM, if you have not already set up SPF you should do so. For a quick introduction to SPF and to get it configured quickly, see Set up SPF in Office 365 to help prevent spoofing. For a more in-depth understanding of how Office 365 uses SPF, or for troubleshooting or non-standard deployments such as hybrid deployments, start with How Office 365 uses Sender Policy Framework (SPF) to prevent spoofing. Next, see Use DMARC to validate email in Office 365. Anti-spam message headers includes the syntax and header fields used by Office 365 for DKIM checks.